
Attackers can power Amazon Echos to hack themselves with self-issued instructions

T3 Journal/Getty Photographs
Educational researchers have devised a brand new working exploit that commandeers Amazon Echo good audio system and forces them to unlock doorways, make telephone calls and unauthorized purchases, and management furnaces, microwave ovens, and different good home equipment.
The assault works by utilizing the machine’s speaker to challenge voice instructions. So long as the speech incorporates the machine wake phrase (often “Alexa” or “Echo”) adopted by a permissible command, the Echo will carry it out, researchers from Royal Holloway College in London and Italy’s College of Catania discovered. Even when units require verbal affirmation earlier than executing delicate instructions, it’s trivial to bypass the measure by including the phrase “sure” about six seconds after issuing the command. Attackers also can exploit what the researchers name the “FVV,” or full voice vulnerability, which permits Echos to make self-issued instructions with out quickly lowering the machine quantity.
Alexa, go hack your self
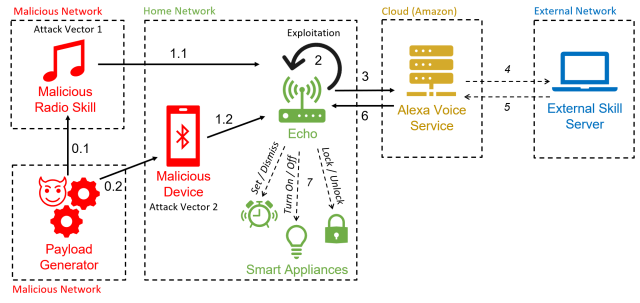
As a result of the hack makes use of Alexa performance to power units to make self-issued instructions, the researchers have dubbed it “AvA,” quick for Alexa vs. Alexa. It requires only some seconds of proximity to a weak machine whereas it’s turned on so an attacker can utter a voice command instructing it to pair with an attacker’s Bluetooth-enabled machine. So long as the machine stays inside radio vary of the Echo, the attacker will be capable of challenge instructions.
The assault “is the primary to use the vulnerability of self-issuing arbitrary instructions on Echo units, permitting an attacker to regulate them for a protracted period of time,” the researchers wrote in a paper printed two weeks in the past. “With this work, we take away the need of getting an exterior speaker close to the goal machine, growing the general probability of the assault.”
A variation of the assault makes use of a malicious radio station to generate the self-issued instructions. That assault is now not potential in the way in which proven within the paper following safety patches that Echo-maker Amazon launched in response to the analysis. The researchers have confirmed that the assaults work towards Third- and 4th-generation Echo Dot units.
Esposito et al.
AvA begins when a weak Echo machine connects by Bluetooth to the attacker’s machine (and for unpatched Echos, after they play the malicious radio station). From then on, the attacker can use a text-to-speech app or different means to stream voice instructions. Right here’s a video of AvA in motion. All of the variations of the assault stay viable, except for what’s proven between 1:40 and a pair of:14:
Alexa versus Alexa – Demo.
The researchers discovered they may use AvA to power units to hold out a number of instructions, many with critical privateness or safety penalties. Attainable malicious actions embody:
- Controlling different good home equipment, similar to turning off lights, turning on a wise microwave oven, setting the heating to an unsafe temperature, or unlocking good door locks. As famous earlier, when Echos require affirmation, the adversary solely must append a “sure” to the command about six seconds after the request.
- Name any telephone quantity, together with one managed by the attacker, in order that it’s potential to listen in on close by sounds. Whereas Echos use a light-weight to point that they’re making a name, units should not at all times seen to customers, and fewer skilled customers might not know what the sunshine means.
- Making unauthorized purchases utilizing the sufferer’s Amazon account. Though Amazon will ship an e-mail notifying the sufferer of the acquisition, the e-mail could also be missed or the person might lose belief in Amazon. Alternatively, attackers also can delete gadgets already within the account procuring cart.
- Tampering with a person’s beforehand linked calendar so as to add, transfer, delete, or modify occasions.
- Impersonate expertise or begin any ability of the attacker’s alternative. This, in flip, may enable attackers to acquire passwords and private information.
- Retrieve all utterances made by the sufferer. Utilizing what the researchers name a “masks assault,” an adversary can intercept instructions and retailer them in a database. This might enable the adversary to extract personal information, collect data on used expertise, and infer person habits.
The researchers wrote:
With these assessments, we demonstrated that AvA can be utilized to offer arbitrary instructions of any kind and size, with optimum outcomes—specifically, an attacker can management good lights with a 93% success price, efficiently purchase undesirable gadgets on Amazon 100% of the instances, and tamper [with] a linked calendar with 88% success price. Complicated instructions that should be acknowledged accurately of their entirety to succeed, similar to calling a telephone quantity, have an nearly optimum success price, on this case 73%. Moreover, outcomes proven in Desk 7 exhibit the attacker can efficiently arrange a Voice Masquerading Assault by way of our Masks Assault ability with out being detected, and all issued utterances could be retrieved and saved within the attacker’s database, specifically 41 in our case.














